One of the core tasks of IT teams in all organizations is ensuring that colleagues have access to the right tools, while also maintaining security by minimizing unnecessary, excessive, or inappropriate access.
In large organizations with extensive IT estates, this can quickly become a hugely laborious process. Today, we’re looking at some of the solutions that exist to help us achieve this by examining the market for access request management software.
Specifically, we’ll be covering:
- What is access request management?
- What does access request management software do?
- 6 access request management tools for 2026
Let’s start with the basics.
What is access request management?
Access request management is the process of receiving, assessing, and responding to requests to access software tools, data, or other resources within our IT environment.
This can look quite different depending on the specific resource that access is being requested for. For instance, the logic for approving a low-risk platform might be relatively simple, but where permissions carry more risk, we’ll generally have more stringent controls.
Or, some resources might not have defined approval rules at all, and decisions will need to be made on a case-by-case basis.
The goal is to ensure that permissions for internal tools and resources are minimized to the users who actually need them.
However, this must be balanced with a few other practical concerns. A key issue here is avoiding unnecessary disruption. So, we need to ensure that access is granted to approved tools with a reasonable turnaround time.
Similarly, software licenses cost money. By minimizing permissions for tools to the colleagues that actually need them, access request management can also help us reduce our spending on licenses and seats.
What does access request management software do?
Understanding what access request management achieves at a high level, we can next move on to how specific software tools can help us to achieve this. There are a couple of broad categories of tools that we’ll need to think about under this umbrella.
Firstly, we have identity management and access management tools. These deal with the actual credentials that users use to access resources, as well as providing admins with a solution to manage and automate the creation, assignment, and lifecycle management of these credentials.
For example, when a colleague joins or leaves the team, or changes roles.
Often, this means using an SSO provider or other identity management tool to handle authentication for software tools and granting or denying access within this.
However, many teams find that an additional workflow layer is required on top of this to ensure that business rules are enforced and tracked effectively.
There are a couple of key ways that this can be achieved. Firstly, many teams opt to handle this within an existing ticketing system or ITSM platform. Many tools in this space offer dedicated access request management capabilities, and even identity management.
Alternatively, for teams with more complex workflow requirements, more customizable workflow management tools that integrate with identity providers may be a better fit, providing more flexibility to enforce the exact business rules and logic that teams require.
This is especially important in cases where access might be granted via multiple channels, including identity management tools, in addition to other methods, such as manual account creation or data retrieval.
What to look for in an access request management tool
Before we start looking at the specific software solutions that are available to help us manage access requests, it’s also important to have a clear picture of the key considerations and decision points we’re likely to encounter when assessing individual platforms.
Arguably, the most pressing issue here is integrations. Firstly, if we’re adopting an entirely new identity management tool, this will need to be supported by the software tools we want to manage access for.
Similarly, if we opt to use a ticketing system or custom workflow solution on top of this, we’ll need to ensure that this integrates with our existing identity management platform, as well as any other tools we’ll need to grant access to resources.
We’ll also need to consider how this integrates with our wider support and ITSM processes, especially given that many users may submit an issue without realising that the appropriate resolution to this is being granted access to a particular platform.
As a core goal of access request management is to reduce the resources required to enforce defined business logic for granting access, another key factor here is automation capabilities. For example, the ability to triage incoming requests automatically and route them to the appropriate queues.
Today, many teams rely on a combination of traditional automations and AI agents to achieve this. Take a look at our guide to low-code AI agent platforms to learn more.
There are also important considerations that stem from the fact that access requests carry important security implications.
Therefore, we’ll want to consider the authentication and authorization tools available in specific platforms, how we can control which users can see specific data, how we log and monitor decisions, how and where our data is stored, and more.
Lastly, as with any software procurement decision, we’ll want to consider costs and licenses. This is a particularly complex question in the case of access request management tools, as the type of solution that’s most cost-effective can vary greatly, depending on our existing software stack and the level of maturity of our IT operations more generally.
For example, if we already use an off-the-shelf tool for related processes that’s able to meet our requirements, this will often be the easiest option to adopt, but wholesale adoption of a similar platform for the sole purpose of managing access requests might not be cost-effective for another team.
These are some of the considerations that we keep in mind as we assess the access request management tools that are available on the market today.
6 access request management tools for 2026
With a strong grasp of what access request management tools achieve and some of the key decisions we’ll need to make when assessing individual solutions, we can move on to examining some of our specific options across the market.
As we said earlier, there are a few distinct categories of tools that we might consider here. Often, to achieve our desired workflows, we might require a combination of tools from these different categories.
To reflect this, we’ve chosen a range of tools that reflect this variety and the different configurations we might opt for to manage access requests.
Our picks are:
Let’s check each one out in turn.
1. Budibase
Budibase is the all-in-one open-source AI workflow toolkit for building Agents, Apps, and Automations, using any data, LLM, or API. IT teams in all industries choose Budibase to transform day-to-day workflows, without compromising on security.
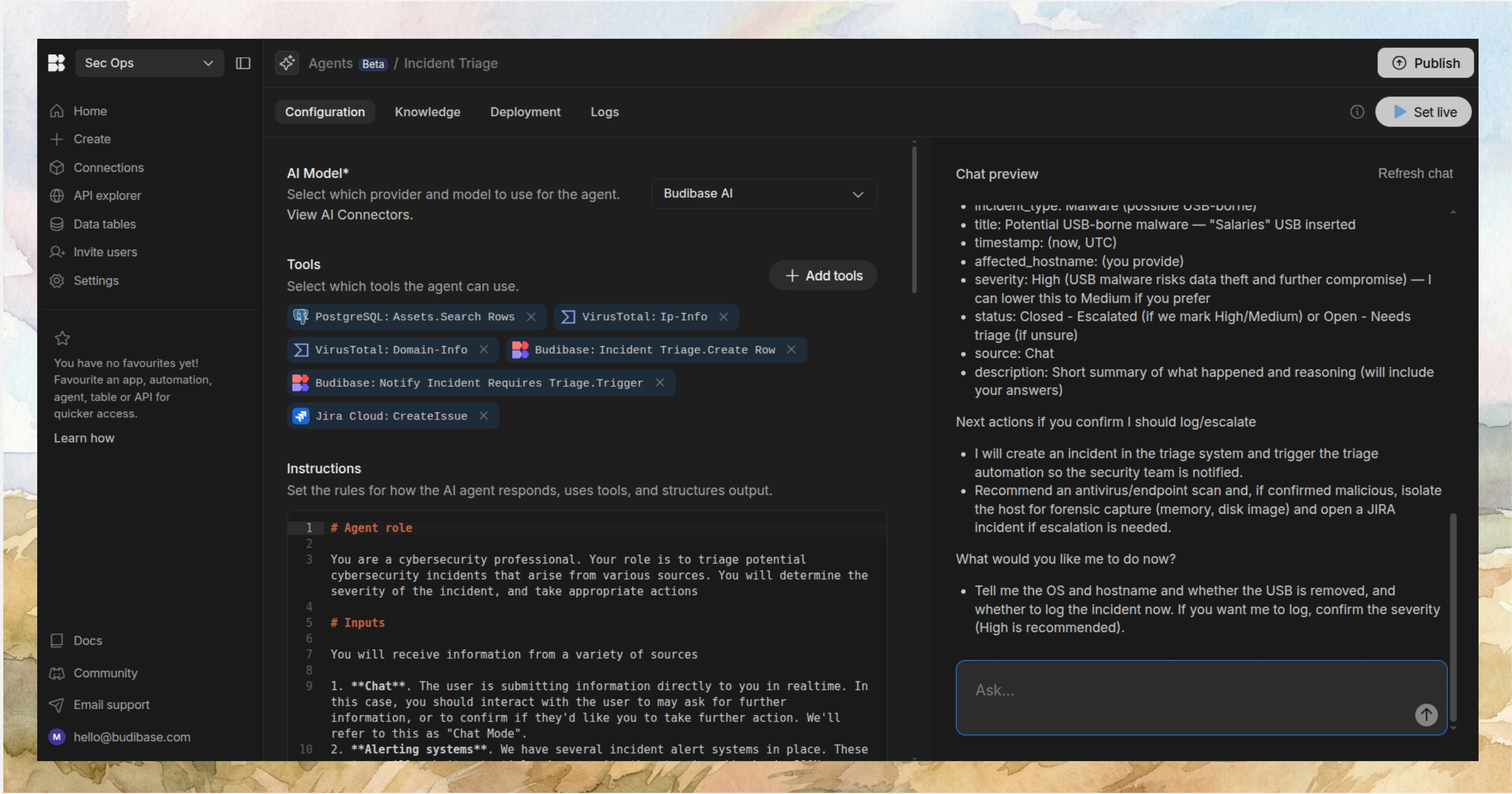
Features
Budibase Agents are instruction-led and model-agnostic. This means you can choose any model with an OpenAI-compatible API, and automate complex business rules in natural language, including tool use and data retrieval. Agents can be invoked via Budibase Automations or existing chat apps like Slack and Discord.
Our platform is fully optimized for teams that need to adopt AI alongside their existing tool stacks. We offer dedicated connectors for a huge range of databases, ready-to-use REST templates for common software tools, including identity managers and ITSM platforms, and custom API requests.
With our leading low-code app builder, Budibase is also ideal for enabling humans to work alongside AI within secure processes. Use Budibase Agents to assess incoming issues, automatically resolve routine requests, and retain human approval steps where you need to.
Use cases
Our users choose Budibase to handle all kinds of IT and operations workflows, including ticketing, approvals, and service request management. Budibase Apps, Agents, and Automations can interact seamlessly, making it the ideal solution for implementing AI in real-world workflows, without sacrificing human control.
Budibase is also highly suited to security-focused, highly regulated teams. With optional self-hosting, custom RBAC, SSO, air-gapped deployments, and support for a range of data sources and LLMs, it’s the ideal solution for powering workflows with AI, without giving up control of your data.
Take a look at our Agents overview to learn more.
2. Okta
Okta is one of the best-known solutions on the market today for identity and access management, providing a secure, centralized experience for managing credentials and access for users to access systems across our software portfolio.
 (Okta Website)
(Okta Website)
This centers around a widely-supported SSO provider that enables users to log in to a huge range of platforms with a single set of credentials. Importantly, Okta also provides password management capabilities for tools that don’t support its SSO tools.
On top of this, Okta offers a range of solutions, including adaptive MFA, security tools for AI agents, identity threat protection, customer identity management, privileged access, and more.
From a request management point of view, Okta offers a few important capabilities. There are dedicated lifecycle management and identity governance tools for IT teams to streamline the process of provisioning access to software tools.
This also includes a no-code workflow builder, complete with a range of customizable templates for common tasks.
Okta also provides a comprehensive API, providing access to trigger functions via external platforms. This makes it a good choice if we want to use Okta to provide identity management capabilities, but build our wider workflows via a separate platform. For example, triggering resolution actions in Okta via a wider service request automation solution.
On the whole, Okta is a highly capable platform, whether used as a sole identity and access management tool or as part of a wider access request management workflow solution.
3. ManageEngine
Next up, we have ManageEngine. This is a comprehensive ITSM and ITOps platform, complete with a range of identity management, governance, and administration tools.
 (ManageEngine Website)
(ManageEngine Website)
This positions ManageEngine as a good fit for teams that want to manage access requests within the same platform that they manage their wider service portfolio and support processes, with more comprehensive identity management capabilities than many other ITSM solutions.
More specifically, ManageEngine provides built-in tools for Active Directory and Microsoft 365 administration, privileged access management, an enterprise password manager, and identity management, complete with SSO and MFA.
This means that access to integrated tools can be managed fully within the ManageEngine platform.
On top of this, ManageEngine more broadly is a highly effective tool for handling a range of IT processes, including dedicated tools for service management, endpoint management, asset management, IT operations, and security information and event management.
There’s also the AppCreator low-code platform for creating custom workflow automations. Alongside its off-the-shelf processes, this positions ManageEngine as a flexible solution for handling a range of request workflows within IT teams.
As such, it has the potential to be a powerful solution for access request management, although this may be a more attractive option if we’re looking to adopt an access request management solution as part of a broader IT platform.
4. Jira Service Management
Jira Service Management is another major player in the ITSM space that’s also a strong choice for handling access request management.

(Jira Service Management Website)
Jira Service Management seeks to provide a unified, streamlined platform for managing all kinds of IT and other internal services. This includes a huge range of capabilities for request management, change management, configuration management, asset management, incident management, and a wide range of other ITSM processes.
Within this service management space, Jira is a popular option for combining customization and configurability with tools and processes that work off-the-shelf. For instance, it offers a wide range of customizable templates for common ITSM workflows and other use cases.
As with many other platforms in this space, Jira Service Management also offers a range of capabilities for adopting AI within service management workflows, including for automatically resolving routine requests.
As part of the wider Atlassian ecosystem, Jira Service Management also integrates closely with Atlassian Guard. This is a comprehensive identity and access management solution, offering centralized admin, SSO, user provisioning, and other capabilities across Atlassian tools.
However, it’s worth noting that Atlassian Guard bills separately for most Jira Service Management plans.
Like ManageEngine, Jira Service Management could be a strong option for teams that want to adopt an access request management solution as part of a wider ITSM platform.
5. Microsoft Entra ID Governance
Entra ID Governance is Microsoft’s identity governance solution, enabling teams to automate the process of granting access to users.
 (Microsoft Website)
(Microsoft Website)
The goal is to automate the lifecycle management tasks for identity management, including automatically creating employee identities via integrations with HR platforms, and automatically assigning permissions and access based on group membership.
As you’d expect, Entra ID Governance offers particularly close integration with other Microsoft tools, especially the wider Entra Suite, including solutions for managing access to devices, and for AI agents to access software tools.
Notably, there are also similar tools for managing access for external users, including suppliers, customers, and partners.
Entra ID Governance also stands out for its AI-driven capabilities, including access reviews. These help to ensure that permissions and access across the organization continue to reflect the needs of real-world users.
As such, Entra ID Governance is a great choice for teams that need a secure platform to automate provisioning and identity lifecycles.
However, if we specifically want a solution that integrates access request management within our wider ITSM processes, we may wish to consider other options.
6. midPoint
Lastly, we have midPoint. This is an open-source identity security platform, offering tools for identity management, governance, and administration that can be hosted in the cloud or on-premises.
 (midPoint Website)
(midPoint Website)
This includes tools for a wide range of identity management tasks, including provisioning and deprovisioning, policy and role management, access certification, lifecycle management, and more.
It’s also an impressive platform from the point of view of analytics, including AI capabilities for identifying potential vulnerabilities. We can also run simulations within midPoint, enabling us to test possible actions, without affecting production states.
It also offers license management capabilities, including tools for monitoring licenses, automating removal, and enforcing approval logic within self-service workflows.
midPoint is an effective solution for handling access request workflows via a user-friendly role catalog. Users can also self-serve on related workflows, including password resets and identity recovery.
On top of this, as an open-source solution, midPoint is a good fit for highly regulated teams, as well as offering compliance with a range of standards, including GDPR, ISO 27001, and others.
As such, it’s a strong option for teams that want to adopt a robust access management tool, although it’s worth noting that we might want to look elsewhere for additional features, such as more in-depth workflow customization or a dedicated identity provider.
The all-in-one open-source AI workflow toolkit
Budibase is the all-in-one open-source AI workflow toolkit that enables teams to build custom Agents, Apps, and Automations on top of any database, LLM, or API.
Take a look at our Agents overview to learn more.